In our previous deep dive on infrastructure trends, we explored the physical and logical transformations happening beneath the AI hype—disaggregated compute, liquid cooling mandates, and the rise of sovereign cloud architectures. But infrastructure without security is just expensive liability.
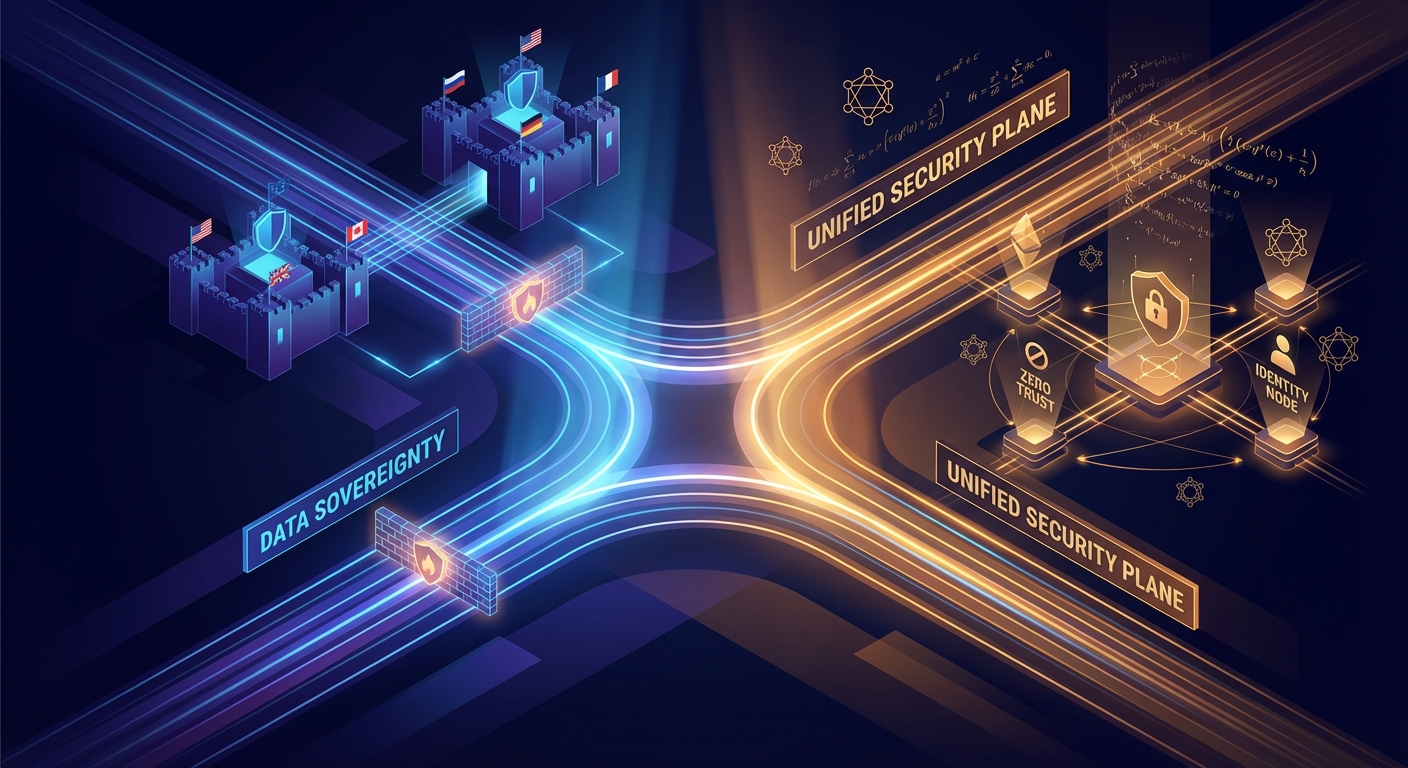
This piece picks up where that one left off. While everyone’s distracted debating AI model capabilities, the security landscape is undergoing what can only be described as a “Great Bifurcation”—a simultaneous fragmentation of the global internet into sovereign, regulated enclaves and a unification of security architectures under converged, identity-centric control planes.
The trends driving this transformation aren’t speculative. They’re rooted in physics, mathematics, and geopolitics—forces that don’t care about hype cycles.
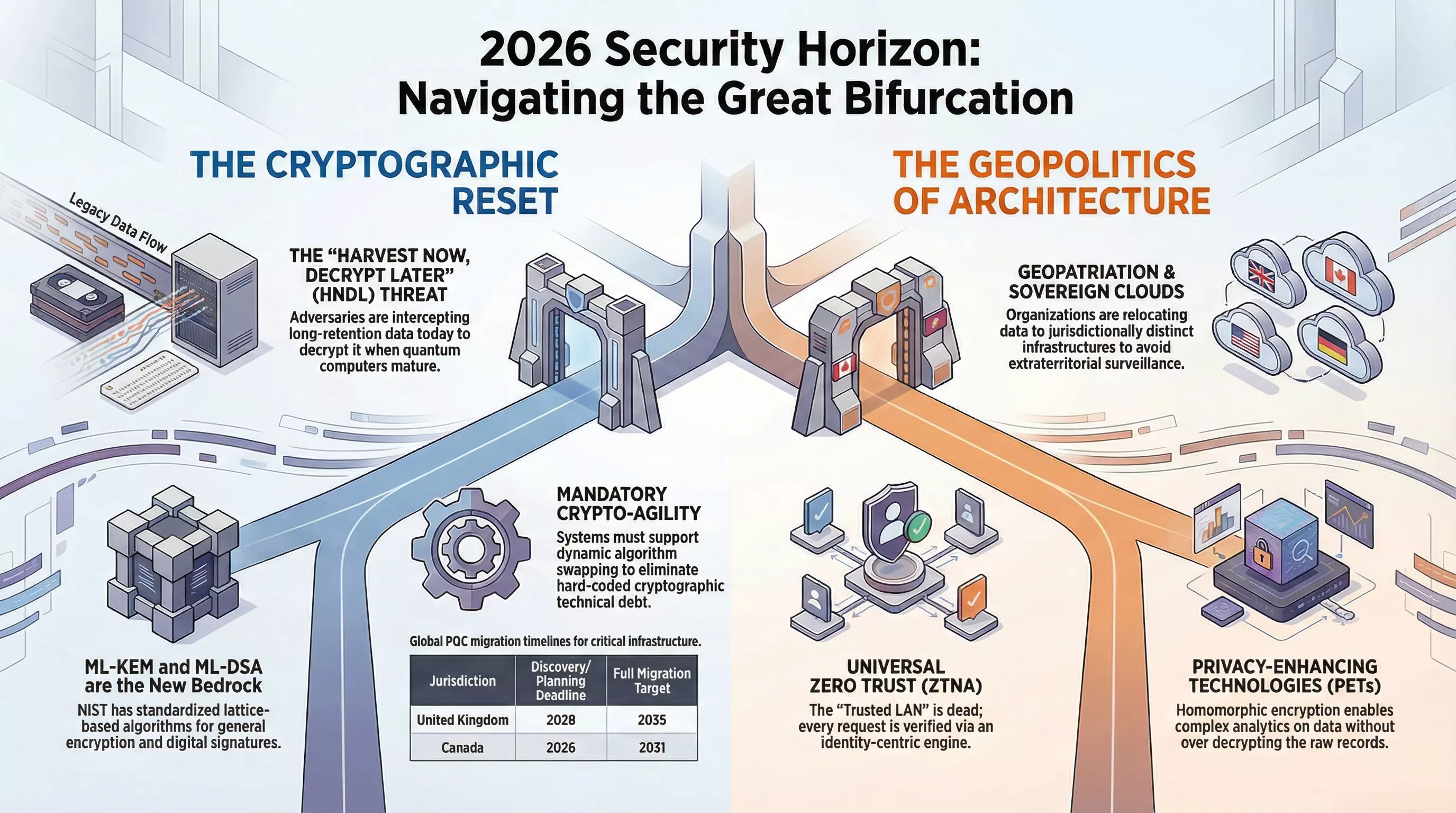
The Cryptographic Reset: Your Encryption Has an Expiration Date
Here’s a reality check that should keep every security leader awake at night: the encryption protecting your most sensitive data today is a depreciating asset with a known expiration date.
The “Cryptographic Reset” isn’t theoretical anymore. NIST has finalized its Post-Quantum Cryptography (PQC) standards, and governments worldwide have published explicit migration timelines. The UK’s National Cyber Security Centre expects critical infrastructure to complete discovery and planning by 2028, finish high-priority migrations by 2031, and achieve full estate migration by 2035. Canada is even more aggressive—federal departments need PQC migration plans in place by April 2026.
Why the urgency? Because of a threat that’s already active: “Harvest Now, Decrypt Later” (HNDL).
Advanced persistent threats and nation-state actors are intercepting and storing encrypted traffic today—diplomatic cables, intellectual property, genomic databases, infrastructure blueprints—with the explicit intention of decrypting it once quantum computers mature. If your data has a confidentiality requirement extending beyond 2030-2035, it’s already vulnerable. The attack isn’t happening in the future; the data collection is happening now.
This fundamentally changes how we think about risk. It’s no longer enough to ask “Is this data secure today?” The question becomes “Will this data remain secure for as long as it needs to be?”
The New Cryptographic Bedrock
NIST’s standardized algorithms—ML-KEM (formerly CRYSTALS-Kyber) for encryption and ML-DSA (formerly CRYSTALS-Dilithium) for digital signatures—are lattice-based mathematical constructs designed to resist both classical and quantum attacks. But here’s what the marketing materials won’t tell you: they’re computationally heavier and produce larger key sizes than their classical predecessors.
This “quantum tax” creates real operational challenges. The combined keys and signatures significantly increase handshake sizes and certificate overhead. For bandwidth-constrained environments—legacy industrial control systems, low-power IoT networks—this can degrade performance or exceed MTU limits, causing fragmentation and latency issues.
The industry response is twofold: Crypto-Agility and Hybrid Architectures.
Crypto-agility means designing systems that can swap algorithms dynamically. Hard-coded cryptographic libraries are now technical debt. Modern systems must be built to pivot if a specific PQC candidate is found vulnerable or as standards evolve.
Hybrid architectures layer classical algorithms with post-quantum candidates. A session key derived from both an Elliptic Curve Diffie-Hellman exchange and an ML-KEM encapsulation ensures data remains secure as long as one of the algorithms holds. If quantum breaks the classical layer, PQC provides defense. If a mathematical breakthrough compromises PQC, the classical layer remains.
On the hardware front, vendors are deploying FPGAs and ASICs specifically tuned for lattice-based cryptography. Solutions like PQShield’s PQPerform-Flare provide dedicated hardware blocks to offload ML-KEM and ML-DSA operations, ensuring firewalls, VPN concentrators, and HSMs maintain line-rate speeds under post-quantum loads. This isn’t optional optimization—it’s mandatory for any organization processing high-volume encrypted traffic.
Data Sovereignty: The Death of the Borderless Internet
The vision of a unified global internet where data flows freely across jurisdictions has effectively ended for enterprise use cases. In its place: the “Splinternet”—a fragmented landscape of compliance regimes, extraterritorial surveillance concerns, and mandatory data localization.
Gartner identifies “Geopatriation” as a top technology trend for 2026—the active relocation of data and workloads from shared global clouds back to jurisdictionally distinct infrastructures. This isn’t paranoia; it’s risk management in response to legal realities like the US CLOUD Act, which grants American authorities access to data held by US companies regardless of where it’s physically stored.
The Sovereignty Stack
True sovereign cloud has matured from marketing buzzword to rigorous technical specification with distinct tiers:
Sovereign Controls involve using global hyperscaler infrastructure while maintaining local control over encryption keys (BYOK/HYOK). The data resides on global servers, but the cloud provider can’t access it in cleartext. Sufficient for some commercial regulated industries, but increasingly viewed as inadequate for critical state data.
Jurisdictional Sovereign Cloud demands physical infrastructure within sovereign territory, operated entirely by a local legal entity subject only to local laws. Critically, the control plane—management interfaces, identity providers, key management systems—must be decoupled from the global mesh. A sovereign cloud in Germany can’t rely on IAM services hosted in the United States. If the global link is severed, the local cloud must remain fully operational.
Air-Gapped Private Sovereign Cloud represents the extreme end: fully isolated environments with no physical or logical connection to the public internet, managed exclusively by cleared local personnel. Reserved for classified national security data and critical infrastructure control systems.
Privacy-Enhancing Technologies as the Bridge
The sovereignty imperative creates a paradox: data must stay local, but insights often require global collaboration. Privacy-Enhancing Technologies (PETs) have gone mainstream as the resolution.
Homomorphic Encryption allows complex analytics and machine learning inference directly on encrypted data without ever decrypting it. A pharmaceutical company in Switzerland can analyze patient data hosted in a US sovereign cloud to identify drug efficacy patterns without raw patient records ever leaving American jurisdiction or being exposed to researchers.
Secure Multi-Party Computation (SMPC) enables multiple parties to jointly compute functions over their inputs while keeping those inputs private. Competing banks can pool transaction data to train fraud detection models without revealing proprietary customer lists or transaction details to each other. The computation happens distributively; no single party ever sees the aggregate dataset.
For enterprise architects, the practical implication is clear: you can no longer deploy uniform global architectures. You must design modular systems that instantiate different security stacks for different regions—full sovereignty controls in restrictive markets, standard public cloud in more permissive jurisdictions.
The Converged Edge: SASE and the Death of the Trusted LAN
The era of fragmented enterprise security—firewalls here, VPN concentrators there, web gateways somewhere else—has ended. Cost pressure, complexity fatigue, and the reality of permanent hybrid work have driven decisive market movement toward Secure Access Service Edge (SASE).
But the most significant evolution isn’t consolidation itself—it’s the expansion of Zero Trust Network Access into Universal ZTNA.
In early implementations, ZTNA primarily replaced remote access VPNs. In 2026, it applies equally to users sitting at desks in corporate headquarters. The local area network is now treated as inherently untrusted.
Plugging into an office ethernet port no longer grants implicit access to the network’s interior. Every access request—whether from a remote coffee shop, a branch office, or the CEO’s desk—passes through the same identity-centric policy engine. The engine verifies user identity, device health posture, and contextual risk before establishing a micro-segmented connection to a specific application.
This eliminates the dangerous “policy gap” where remote users faced strict ZTNA checks while on-premises users enjoyed broad lateral network access. Universal ZTNA ensures consistent security posture regardless of location, dramatically reducing the attack surface for ransomware lateral movement or malicious insiders.
Single-Vendor and the “Coffee Shop” Network
The market has shifted aggressively toward single-vendor SASE stacks. The complexity of stitching together “best of breed” solutions from multiple vendors created operational burden and dangerous visibility gaps.
A unified stack enables “Single-Pass” inspection—a data packet is decrypted once and simultaneously scanned for malware, sensitive data, and access rights before re-encryption. This drastically reduces latency compared to multi-vendor service chaining, where traffic must be decrypted and re-encrypted at multiple hops.
The operational benefit is equally significant: a single control plane allows instant global policy propagation. Update a policy to block a new threat signature or revoke access for a compromised user group, and it propagates to every branch office, remote laptop, and cloud gateway in minutes.
This maturity is enabling the “Coffee Shop” networking model—deprecating expensive private MPLS circuits in favor of commoditized business broadband. The physical network simply provides raw, untrusted internet connectivity. The SASE platform provides the secure overlay. New branch sites can be brought online using any available internet link without waiting months to provision dedicated circuits.
Supply Chain Security: From Awareness to Verification
Following a half-decade of devastating supply chain attacks—SolarWinds, Log4j, XZ Utils—the industry has moved from passive “awareness” to active “verification.” Software Supply Chain Security has become a rigorous discipline underpinned by automation, mandated transparency, and cryptographic provenance.
VEX: Solving the Alert Fatigue Crisis
The widespread adoption of Software Bills of Materials (SBOM) created an unforeseen problem: noise. Security scanners would ingest an SBOM and flag thousands of CVEs within dependencies, burying developers in false positives.
Vulnerability Exploitability Exchange (VEX) has emerged as the solution. VEX allows software vendors to issue machine-readable statements clarifying the actual status of a vulnerability within their product. A vendor can assert: “Yes, CVE-2026-9999 is present in our dependency tree, but the affected function is never loaded or executed by our application—status: Not Affected.”
This context is critical for risk prioritization. In practice, VEX documents are consumed by tools to automatically suppress non-exploitable alerts in CI/CD pipelines and vulnerability dashboards. Major procurers—including the US government and large financial institutions—now require VEX attestations alongside SBOMs as conditions of purchase.
The Living SBOM and SLSA Provenance
The SBOM has transitioned from static compliance artifact to “living graph” monitored by continuous verification platforms. Modern tools maintain dynamic maps of an organization’s entire software estate. When a new vulnerability is disclosed in a low-level library, the system instantly queries this graph to identify every affected application and server—replacing the frantic manual spreadsheets of the past.
Policy-as-Code enforcement ensures insecure software never reaches production. A deployment can be blocked automatically if an artifact lacks a valid SBOM, contains an unmitigated critical vulnerability without VEX suppression, or fails provenance requirements.
The SLSA (Supply-chain Levels for Software Artifacts) framework has become the de facto standard for build integrity. Organizations are adopting hermetic builds—ephemeral, isolated, internet-disconnected build environments where every step is cryptographically signed. This creates an unforgeable chain of custody proving the binary running in production is bit-for-bit identical to the peer-reviewed source code—neutralizing build server injection attacks.
Protecting the Physical-Digital Frontier: OT and IoT
The air gap is a relic. Industrial environments are now hyper-connected, driven by predictive maintenance, remote operations, and process optimization. This exposes critical infrastructure to the full spectrum of cyber threats, prompting a shift toward Cyber-Physical Systems protection and Mesh Security Architectures.
The Purdue Model’s Collapse
The traditional Purdue Enterprise Reference Architecture—rigid hierarchical layers separating field-level sensors from enterprise systems—struggles with modern IIoT realities. Sensors at Level 1 now often communicate directly with cloud analytics at Level 5, bypassing intermediate layers entirely.
The response is a “Hybrid” or “Collapsed” architecture focused on the Secure Industrial DMZ (Level 3.5). This zone acts as a highly monitored airlock where all IT/OT traffic is inspected by protocol-aware gateways capable of interpreting industrial protocols like Modbus, BACnet, or OPC UA. Only valid, safe commands pass through; potentially dangerous operations require multi-party authorization.
Mesh Security for Scale
With over 21 billion active IoT endpoints projected, centralized security appliances become bottlenecks and single points of failure. Mesh Security offers a decentralized alternative.
In a mesh architecture, every network element—switches, wireless access points, edge gateways—becomes a policy enforcement point. If a compromised vibration sensor starts scanning the network, the nearest switch quarantines it at the port level instantly, without routing traffic back to a central firewall. These distributed nodes share threat intelligence in real-time, creating an automated immune system response across facilities.
The Final Frontiers: Space and Subsea
As dependency on global connectivity becomes absolute, the physical infrastructure enabling it—satellites in orbit and cables on the ocean floor—has moved to the center of the security conversation.
Space-Based Zero Trust is now operational reality. Modern LEO satellites are intelligent edge nodes processing data in orbit, requiring continuous mutual authentication. A commandeered or jammed satellite must be dynamically isolated from the mesh to prevent lateral movement or data corruption. Confidential Computing hardware—Trusted Execution Environments—ensures sensitive workloads remain encrypted even while being processed, protecting data even if a satellite’s operating system is compromised.
Subsea cables carry over 95% of international data traffic. The increasing frequency of “accidental” cuts and suspicious naval activity has elevated cable security to top-tier national priority. “Smart Cables” now integrate environmental sensors directly into repeaters, detecting the acoustic signatures of submarines or tampering devices before cuts occur. Regional Cable Security Hubs aggregate this data with AIS ship tracking and satellite surveillance, using AI to detect anomalies—fishing trawlers loitering over critical routes or vessels “going dark”—enabling proactive intervention.
Digital Identity: The Wallet Revolution
The centralized identity model—usernames and passwords in vulnerable corporate databases—is collapsing. It’s being replaced by Decentralized Identity and Self-Sovereign Identity (SSI).
The EU Digital Identity Wallet is now mandatory across member states, allowing citizens to store verifiable credentials (IDs, licenses, degrees) on their devices. This shifts control from issuer to user, enabling “selective disclosure”—proving you’re over 18 without revealing your birthdate, verifying employment without exposing salary history.
For enterprise security, this eliminates the honeypots of personal data that attract hackers. Verifiable Credentials create proofs without creating correlation trails, fundamentally changing how authentication and authorization work.
What This Means for Security Leaders
The security architecture transformation of 2026 demands structural responses, not incremental patches:
Start the quantum migration now. Deploy discovery tools to map all cryptographic dependencies. Identify “long-secrecy” data and prioritize for hybrid PQC migration. This is retrospective defense—the attacks have already started.
Design for sovereignty from day one. Assume data mobility will continue to be restricted. Build modular architectures that can instantiate different security stacks for different jurisdictions without fragmenting operations.
Converge aggressively. Retire point solutions. Universal ZTNA across all edges—including the internal LAN—with single-vendor SASE is the new baseline.
Demand supply chain transparency. Mandate VEX and SBOMs in all procurement. Automate ingestion to reduce vulnerability noise. Make SLSA provenance a non-negotiable.
Extend your threat model. Your risk surface now includes the satellites carrying your data and the subsea cables connecting your offices. These aren’t exotic edge cases—they’re critical dependencies.
The organizations that recognize these shifts—rather than dismissing them as “not our problem” while chasing AI headlines—will build the resilient, trustworthy foundations that actually enable competitive advantage.
Trust isn’t assumed anymore. It’s architected, verified, and continuously validated.