This week, Alberta found itself at the center of a privacy incident that made national headlines. But if you’ve only read the news coverage, you’ve likely missed what actually happened—and more importantly, how it happened from a technical and governance perspective.
Let’s break it down.
What This Wasn’t
First, let’s clear the air: this was not a cyberattack on Elections Alberta’s systems.
Elections Alberta stated explicitly on April 30, 2026 that there had been no breach of its databases or infrastructure. Their systems weren’t compromised. No one exploited a vulnerability, deployed malware, or stole credentials to break in.
This matters because the incident has been discussed in the same breath as ransomware attacks and nation-state intrusions. It’s not in that category. Understanding what it actually was helps us understand what went wrong—and what needs to change.
What Actually Happened
The incident is best understood as a data governance failure and downstream disclosure event.
Here’s the chain of events:
-
Lawful Distribution: Under Alberta’s Election Act, Elections Alberta provides registered political parties with copies of the provincial List of Electors after elections. This is legal and normal.
-
Unauthorized Repurposing: A copy of that list—reportedly provided to the Republican Party of Alberta in 2025—was allegedly used by a third party called the Centurion Project Ltd. to build a publicly accessible, searchable web application.
-
Weak Access Controls: According to Canadian Press reporters who examined the database before it was taken down, the application required no identity verification. Anyone with the link could search it.
-
Exposure of Sensitive Data: The public-facing interface exposed at least names and home addresses. Searches reportedly revealed entries for judges, Crown prosecutors, senators, prominent politicians, journalists, and Alberta’s top elections official.
Elections Alberta identified the issue through an elegant technical control: seeded fictitious voter records. Alberta law explicitly authorizes the Chief Electoral Officer to include fake voters in distributed lists specifically for tracing unauthorized use. Investigators matched those “salted names” in the Centurion database to the Republican Party of Alberta’s 2025 copy.
The Timeline
The response moved fast once Elections Alberta had credible information:
| Date | Event |
|---|---|
| April 27, 2026 | Elections Alberta obtains credible information suggesting Centurion may possess a party-issued list |
| April 28, 2026 | Chief Electoral Officer sends cease-and-desist to individuals associated with Centurion |
| April 29, 2026 | Elections Alberta and Edmonton Police Service attend a Centurion event in Edmonton to ensure service of the directive |
| April 30, 2026 (AM) | Court of King’s Bench grants an ex parte emergent injunction |
| April 30, 2026 (Later) | The elector-list portion of Centurion’s website is no longer accessible |
| April 30, 2026 | RCMP confirms investigation |
From credible information to injunction: three days. That’s actually a solid response timeline for this type of incident.
The Technical Picture
Let’s map this to something security professionals will recognize. The likely attack path wasn’t an “attack” at all—it was authorized-recipient misuse.
The most probable scenario:
- A registered political party received a lawful copy of the elector list
- That list (or a derivative) was transferred or made available outside authorized users
- A downstream holder converted it into a searchable web application
- The application was exposed to anyone with the link
The application itself was reportedly a CRM-style voter identification tool. Centurion described it as a system where supporters could “claim” people they knew, send surveys, and conduct outreach—“building the largest voter identification effort in Alberta’s history,” according to their event materials.
From what’s publicly documented, here’s the technical failure pattern:
| Failure Mode | Evidence | Confidence |
|---|---|---|
| Misuse of legitimately issued dataset by authorized recipient or downstream party | Elections Alberta explicitly states this; seeded records traced to Republican Party copy | High |
| Re-publication of sensitive data into searchable web tool | Canadian Press directly examined the database | High |
| Weak access controls (no authentication, link-accessible) | Canadian Press reported no identity verification required | High |
| Possible third-party data sourcing | Centurion claims they relied on a “third party” for datasets | Moderate |
What we don’t have evidence of: credential theft, exploit-driven compromise, malware, or any named CVE exploitation. This wasn’t a hack—it was a governance failure.
What Was Exposed
Alberta’s List of Electors contains:
- First names, middle names, surnames
- Address and postal code
- Telephone number
- Unique identifier number
- Electoral division and voting area
The public-facing Centurion application reportedly exposed names and home addresses. Centurion later claimed volunteers didn’t have access to phone numbers or emails—but that claim hasn’t been independently verified.
What makes this particularly concerning isn’t just the data itself. It’s who was in the database. Canadian Press reported finding:
- Judges
- Crown prosecutors
- Senators
- Prominent politicians
- Journalists
- Alberta’s Chief Electoral Officer
For these categories, home address exposure creates elevated physical security risks: stalking, harassment, doxxing, intimidation, swatting, and highly targeted social engineering attacks.
Understanding the Political Ecosystem
To understand how data flows—and leaks—in Alberta’s political landscape, it helps to visualize the structure. Political organizing in the province operates across three distinct tiers, each with different levels of regulation and data access.
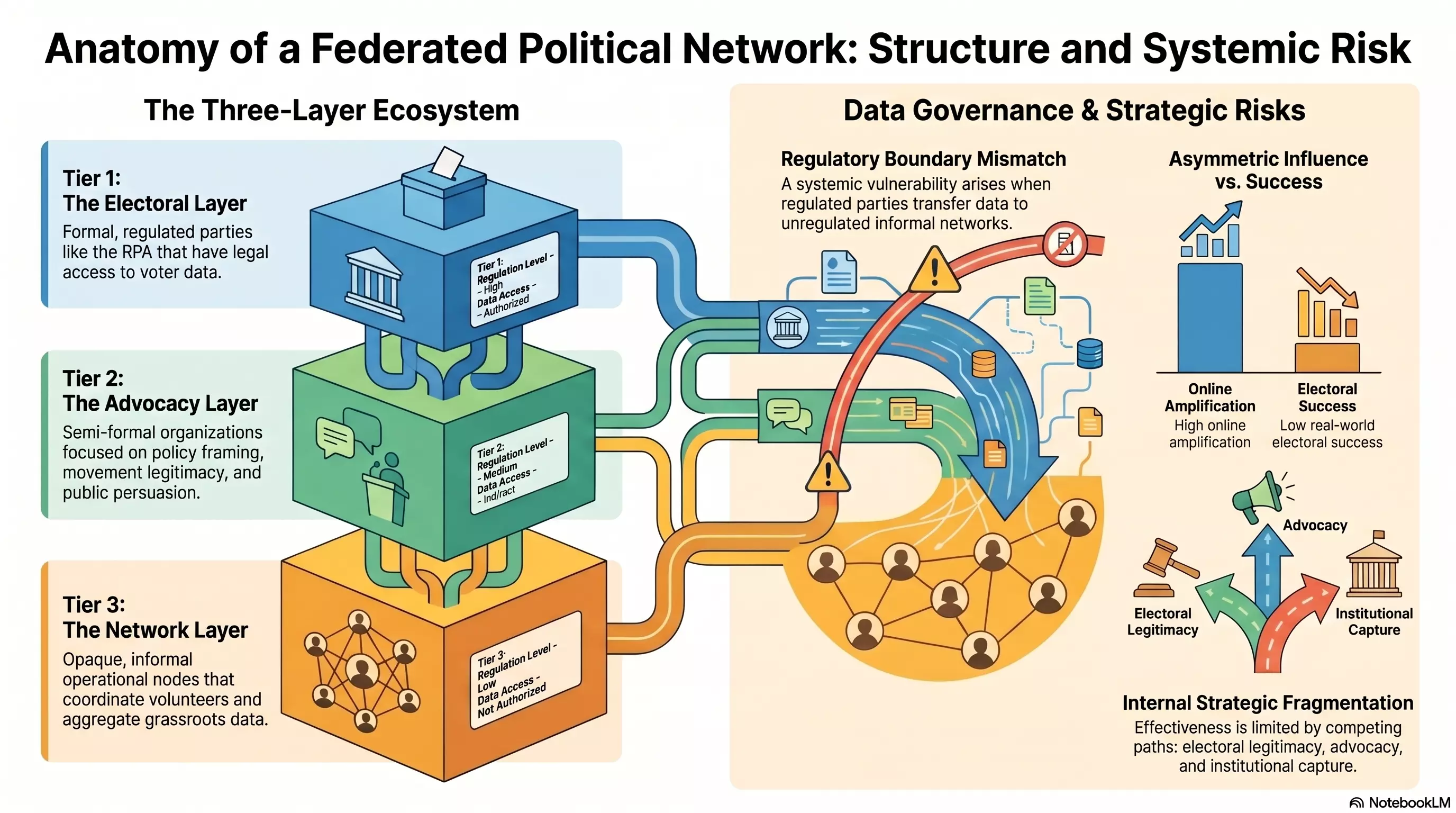
Tier 1: The Electoral Layer — Formal, registered political parties like the Republican Party of Alberta. These are heavily regulated entities with legal access to voter data under the Election Act. High regulation, authorized data access.
Tier 2: The Advocacy Layer — Semi-formal organizations focused on policy framing, movement legitimacy, and public persuasion. Medium regulation, indirect data access.
Tier 3: The Network Layer — Opaque, informal operational nodes that coordinate volunteers and aggregate grassroots data. Low regulation, not authorized for direct data access.
The systemic vulnerability here is the regulatory boundary mismatch: when regulated parties transfer data to unregulated informal networks, accountability breaks down. The Centurion Project appears to sit somewhere in Tier 2 or 3—close enough to a registered party to receive data, but operating outside the regulatory framework that governs how that data should be protected.
This tiered structure also creates strategic fragmentation: organizations split between pursuing electoral legitimacy, advocacy influence, and institutional capture often have competing priorities—and inconsistent data handling practices.
The Regulatory Gap
Here’s where it gets interesting from a governance perspective.
Alberta’s Privacy Commissioner, Diane McLeod, noted that Alberta’s Personal Information Protection Act (PIPA) does not apply to political parties. She renewed calls for parties to be brought under PIPA—a recommendation the Office of the Information and Privacy Commissioner had already made in its 2024 PIPA review submission.
So we have a situation where:
- The Election Act imposes duties and penalties on party handling of elector data
- But the broader private-sector privacy framework doesn’t cover parties the same way it covers businesses
- Parties receive extremely sensitive datasets (names, addresses, phone numbers, unique IDs)
- Controls on downstream use are… variable
This regulatory gap is arguably the root cause. The Election Act requires parties to “take all reasonable steps” to protect the list and immediately notify the Chief Electoral Officer if it’s lost. Contravening these sections is punishable. But there’s no equivalent to the broader accountability frameworks that apply to private-sector data handlers.
What Good Controls Would Look Like
Elections Alberta actually publishes guidance on minimum safeguards for elector list handling. Their recommendations include:
- Designated custodian: Someone formally responsible for the data
- Least-privilege access: Only people who need it should have it
- Password protection: Encrypted electronic copies
- Limited reproduction: Don’t make unnecessary copies
- Secure storage: Physical and digital
- Signed user declarations: Acknowledgment of obligations
- Secure destruction: When you’re done with it
- Immediate loss reporting: If something goes wrong, say so immediately—with details
These are reasonable baseline controls. The question is whether they were followed, and whether they’re sufficient for data this sensitive.
Going forward, Elections Alberta should consider:
- Per-recipient cryptographic watermarking or row-level provenance tagging
- Controlled portal access rather than downloadable flat files
- Mandatory short-lived access tokens
- Machine-readable access logs for all list deliveries
- Stronger contractual/attestation controls
On the party side, the baseline should be enterprise-grade:
- MFA on every account touching elector data
- DLP rules for exports and email forwarding
- Encrypted storage with audit retention
- Explicit vendor due diligence
- Breach notification obligations measured in hours, not days
Open Questions
As of April 30, 2026, several important questions remain unanswered:
- Chain of custody: Exactly how did the data move from the Republican Party copy to the Centurion application?
- Full exposure scope: Did the backend store unique elector IDs, phone numbers, or other fields not visible in the public interface?
- Access extent: How many people accessed or copied the data before takedown?
- Third-party involvement: Centurion referenced a “third party” data source—was this a data broker, contractor, or transformed export from the authorized copy?
Elections Alberta said they’re still working with law enforcement and the Privacy Commissioner to determine scale and scope.
The Takeaway
This incident is a textbook example of why data governance matters as much as perimeter security.
Elections Alberta’s systems weren’t breached. Their technical controls—including the seeded fictitious voters—actually worked exactly as designed for tracing unauthorized use. The failure happened downstream, in the gap between “lawful distribution to a political party” and “publicly searchable web application.”
For organizations handling sensitive data, the lesson is clear: your security posture isn’t just about keeping attackers out. It’s about maintaining control and accountability across the entire data lifecycle—including what happens after you legitimately share data with authorized recipients.
And for legislators and regulators: maybe it’s time to close that political-party privacy gap.
This analysis is based on official Elections Alberta releases, Canadian legal texts, and direct reporting from Canadian Press and other outlets who examined the database before it was taken down. The RCMP investigation is ongoing.